Senior Principal Researcher, Microsoft Research
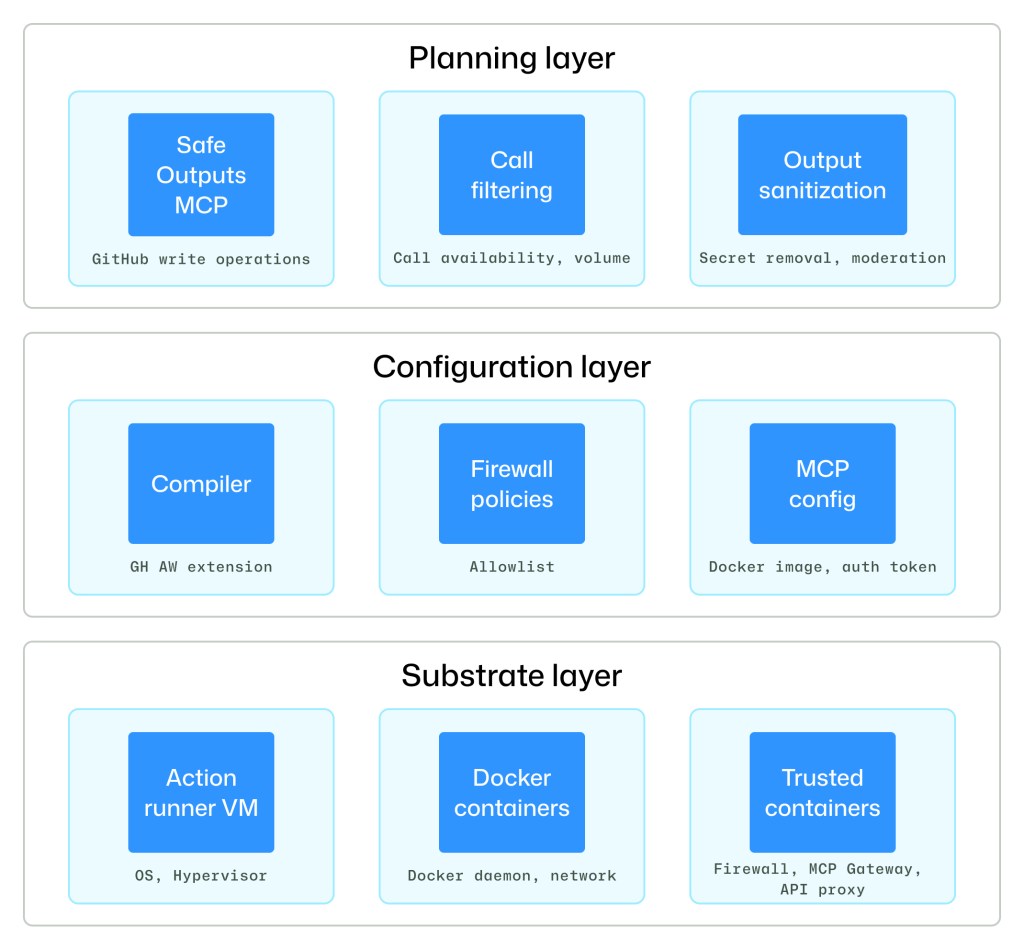
Under the hood: Security architecture of GitHub Agentic Workflows
GitHub Agentic Workflows are built with isolation, constrained outputs, and comprehensive logging. Learn how our threat model and security architecture help teams run agents safely in GitHub Actions. The post Under the hood: Security architecture of GitHub Agentic Workflows appeared first on The GitHub Blog.
Article sourced from GitHub Blog
View original articleRelated Articles
Full Disclosure: A Third (and Fourth) Azure Sign-In Log Bypass Found
Trusted Security researchers have identified two new techniques for bypassing Azure sign-in logging, adding to previously known vulnerabilities in Microsoft's cloud authentication system. These bypasses are particularly concerning because they allow attackers to hide their activities from audit logs that organizations depend on for security monitoring and regulatory compliance. The disclosure highlights an ongoing pattern of logging vulnerabilities in Azure that requires urgent attention.
US Takes Down Botnets Used in Record-Breaking Cyberattacks
US law enforcement has shut down four major botnets—JackSkid, Mossad, Aisuru, and Kimwolf—collectively comprising over 3 million compromised devices. Aisuru and Kimwolf were particularly notorious, having executed a record-breaking 31.4 terabit-per-second DDoS attack in November. The operation involved the Department of Justice, Defense Criminal Investigative Service, and international partners from Canada and Germany.

A rogue AI led to a serious security incident at Meta
Meta disclosed that an AI agent caused a security incident by posting inaccurate technical advice to an internal forum, which an employee then acted upon, temporarily exposing sensitive company data. While Meta claims no user information was compromised, the incident marks the second AI-related problem at the company in recent weeks, raising concerns about autonomous AI systems operating in corporate environments.